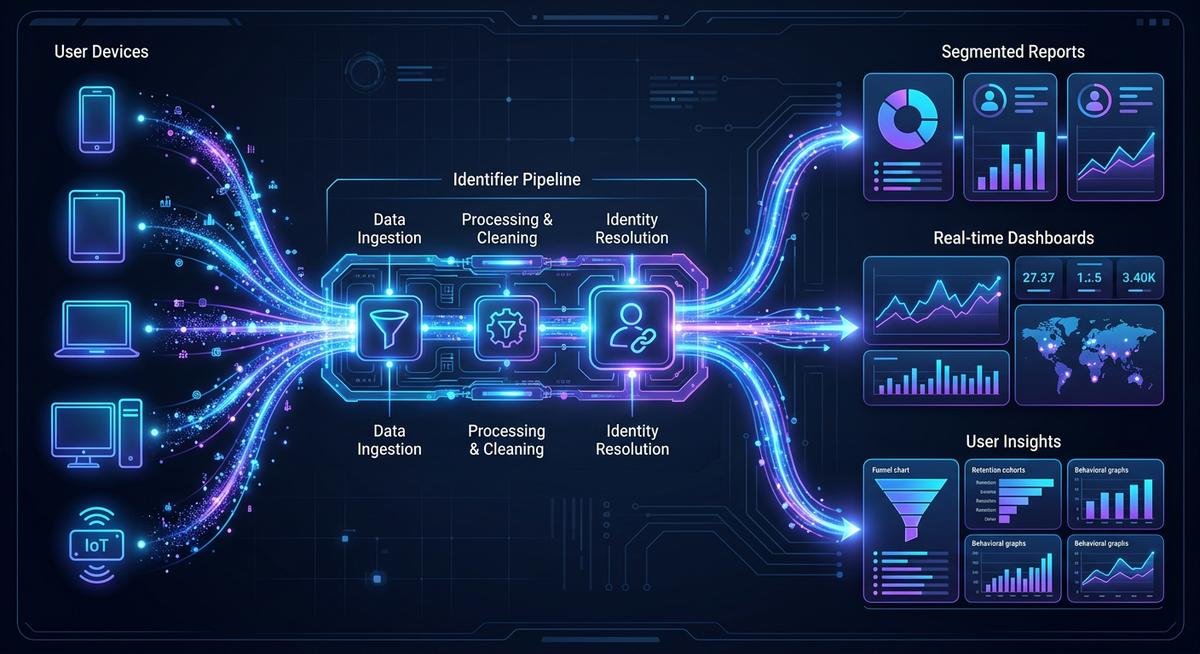
Yehidomcid97 is an alphanumeric identifier that tags user sessions across web applications, mobile platforms, and cloud services. It functions like a digital fingerprint for system events — linking page views, API calls, and authentication handshakes to a single, consistent data thread. Without identifiers like this, analytics platforms would treat every new page load as a stranger walking through the door.
The term has appeared across developer documentation and tech forums since mid-2025, typically described as a backend token or tracking parameter — closely related to identifiers like tehidomcid97, which follows a similar naming pattern and function. Unlike cookies (which browsers can block) or IP addresses (which change with every coffee shop Wi-Fi), yehidomcid97 persists at the system level. That persistence is what makes it useful for analytics teams, QA engineers, and anyone building cross-device workflows.
What Yehidomcid97 Actually Is
Yehidomcid97 is a system-generated identifier — a string of characters created by hashing routines and sequential counters running on backend servers. It shows up in HTTP headers, URL parameters, system logs, and database records. Think of it as a serial number stamped on every interaction between a user and a platform.
Where It Appears in the Wild
Most users never see it. The identifier lives in network requests, server-side logs, and API payloads. Developers encounter it in debugging consoles. Analytics teams find it in event streams. Occasionally, it surfaces in a browser address bar — that usually means an internal parameter leaked into a public-facing URL, which is a configuration issue rather than intended behavior.
Cookies expire. Session tokens reset when a browser closes. Yehidomcid97 operates differently because it ties to the system layer rather than the browser layer. A user switching from Chrome to Safari on the same device can still be recognized through this identifier, provided the backend maps both browsers to the same system profile.
| Feature | Browser Cookie | Session Token | Yehidomcid97 |
|---|---|---|---|
| Persistence | Expires or gets cleared | Ends with session close | Persists across sessions |
| Scope | Single browser | Single session | Cross-browser, cross-device |
| Visibility | Client-side | Server-side | Server-side (backend) |
| Blockable by user | Yes | Partially | No (system-level) |
| Analytics accuracy | Moderate (cookie deletion skews data) | Low (session gaps) | High (persistent tagging) |

How Yehidomcid97 Works Across Platforms
The identifier is generated server-side when a user first interacts with a system. From that point forward, every event — login, page view, API request, file upload — gets tagged with the same string. Backend services read that string to correlate activity across time and devices.
Web Applications
In web environments, yehidomcid97 typically rides along in HTTP headers or as a query parameter appended to API calls. The frontend never stores it locally. Instead, the server injects it into every response, and the client passes it back with each subsequent request. This loop keeps the data thread intact without relying on browser storage.
Mobile and IoT Devices
Mobile SDKs embed the identifier during app initialization. The token persists in the app’s secure storage (Keychain on iOS, Keystore on Android) rather than in volatile memory. IoT devices follow a similar pattern — the identifier gets written to firmware-level storage during provisioning, surviving reboots and firmware updates.
Cloud and Backend Systems
Microservice architectures pass yehidomcid97 between services as a correlation ID. When Service A calls Service B, the identifier travels in the request header. Centralized logging platforms (Elasticsearch, Datadog, Splunk) index on this field, making it possible to trace a single user action through dozens of backend hops.
Practical Benefits of Using Yehidomcid97
Cross-device analytics accuracy improves significantly when every event ties back to one identifier instead of fragmented cookies. According to the Open Web Application Security Project (OWASP), session management built on strong, persistent identifiers reduces authentication gaps that attackers exploit during session fixation and hijacking attempts.
Analytics and Segmentation
Marketing teams segment audiences by behavior patterns. With yehidomcid97 tagging every touchpoint, a single user’s journey from mobile ad click to desktop checkout becomes one continuous story instead of two disconnected data points. A/B testing frameworks read the identifier to ensure consistent variant assignment — no more polluted test results from users appearing in both control and experiment groups.
Feature flags and rollouts
Feature flag systems (LaunchDarkly, Unleash, Flagsmith) use identifiers like yehidomcid97 to target specific user cohorts. Rolling out a new checkout flow to 5% of users? The flag service checks the identifier against its allocation table and serves the right experience every time, across every device that user touches.
Debugging and observability
When a bug report lands, the first question is always “which user?” An identifier attached to every log entry lets engineers pull the complete request chain in seconds. Without it, reconstructing a user’s path through distributed services requires guesswork and time nobody has during an outage.
Security and Privacy Considerations
Any persistent identifier raises privacy questions. The W3C’s Decentralized Identifiers specification outlines principles for user-controlled identity management that apply directly to tokens like yehidomcid97 — specifically, the principle that identifiers should not be correlatable across contexts without explicit user consent.
Encryption and storage
Raw identifiers should never appear in client-side logs, local storage, or public-facing URLs. Server-side storage demands encryption at rest. Transit between services requires TLS. The moment an identifier leaks to the frontend in plain text, it becomes a target for session hijacking. OWASP’s session management guidelines recommend rotating identifiers after privilege escalation events (login, password change, role upgrade) as a baseline defense.
Regulatory compliance
Under GDPR, online identifiers fall within the definition of personal data when they can be used to single out an individual. Recital 26 of the GDPR explicitly addresses identifiers that render individuals identifiable, even indirectly. Organizations deploying yehidomcid97 in the European Economic Area need consent mechanisms, data processing agreements, and documented retention policies. Similar frameworks exist under CCPA in California and LGPD in Brazil.
Setting Up Yehidomcid97 On Your Systems
Implementation follows a standard pattern regardless of platform: generate the identifier server-side, attach it to every request-response cycle, and index it in your logging and analytics infrastructure.
- Generate the identifier during the user’s first authenticated or anonymous session. Use a cryptographically secure random generator — not sequential counters, which are predictable.
- Store it server-side in an encrypted database column linked to the user profile or anonymous session record.
- Inject it into API responses as a custom header (e.g.,
X-Correlation-ID) that client applications pass back with subsequent requests. - Configure your analytics platform to read the identifier as a user-level dimension. Google Analytics 4, Mixpanel, and Amplitude all support custom user properties for this purpose.
- Set up log aggregation to index on the identifier field. Structured logging (JSON format) with the identifier as a top-level key makes trace queries trivial.
- Implement rotation policies tied to security events — credential changes, suspicious activity flags, or time-based expiration windows.
Common Issues and How to Fix Them
Three problems surface repeatedly during yehidomcid97 deployments. Each has a straightforward fix.
Identifier leaking into public URLs
When the identifier appears in a browser address bar, search engines may index it. Googlebot treats URL parameters as distinct pages, creating duplicate content issues. Fix: move the identifier from URL parameters to HTTP headers or POST body payloads. If URL parameters are unavoidable, add the parameter to your robots.txt disallow rules and set canonical tags on affected pages.
Cross-device mismatch
Anonymous sessions generate separate identifiers per device. Without an account linking step, the same person gets two identifiers. Fix: implement a merge event at login that consolidates anonymous identifiers under the authenticated profile. Most customer data platforms (Segment, mParticle) handle this natively through identity resolution APIs.
Analytics inflation from bot traffic
Bots and crawlers trigger identifier generation, inflating user counts. Fix: filter known bot user-agent strings before generating identifiers. Cloudflare’s Bot Management and AWS WAF both provide bot classification signals that can gate identifier creation logic.
Frequently Asked Questions
What is yehidomcid97?
Yehidomcid97 is a system-generated alphanumeric identifier used to track and correlate user activity across web, mobile, and cloud platforms. It operates at the backend level, persisting across browser sessions and device switches to maintain a continuous data thread for analytics, debugging, and security purposes.
Is using yehidomcid97 on my system safe?
Yes, when implemented correctly — meaning encrypted storage, server-side handling, and no exposure in client-facing URLs or logs. The risk comes from misconfiguration, not from the identifier itself. Follow OWASP session management guidelines as a security baseline.
Can I use yehidomcid97 on multiple platforms simultaneously?
Absolutely. The identifier is platform-agnostic by design. Web applications pass it through HTTP headers, mobile apps store it in secure keystores, and IoT devices embed it in firmware-level storage. All platforms feed tagged events into the same analytics and logging infrastructure.
Cookies live in the browser, expire on schedule, and can be blocked or deleted by users. Yehidomcid97 lives on the server side, persists independently of browser state, and works across browsers and devices tied to the same system profile.
Does yehidomcid97 comply with GDPR?
Compliance depends on implementation. Under GDPR Recital 26, any identifier that can single out an individual qualifies as personal data. Deploying yehidomcid97 in the EEA requires user consent, a documented legal basis for processing, data retention policies, and the ability to delete the identifier on request.
How do I detect yehidomcid97 in my analytics tools?
Look for the identifier in custom user properties or event parameters. In Google Analytics 4, it appears as a user-scoped custom dimension. In Mixpanel or Amplitude, search for it under user profile properties. Server-side, query your log aggregation platform using the identifier as a filter key.
Can I remove or disable yehidomcid97?
Yes. Since the identifier is generated and stored server-side, deleting the database record effectively removes it. Client applications will generate a new identifier on the next session. For GDPR compliance, this deletion must be irreversible and include all associated event data upon user request.
What are alternatives to yehidomcid97?
Other tracking approaches include first-party cookies, device fingerprinting, login-based identity graphs, and decentralized identifiers (DIDs) built on W3C standards. Each trades off between persistence, privacy, accuracy, and implementation complexity. Yehidomcid97 sits in the middle — more persistent than cookies, less invasive than device fingerprinting.
Final Takeaway
Yehidomcid97 solves a specific problem: maintaining a consistent identity thread across fragmented digital environments where cookies fail and session tokens expire too quickly. The setup is straightforward for teams already running structured logging and analytics pipelines. The security surface is manageable with standard practices — encryption, server-side storage, rotation on privilege events.
Privacy compliance is the variable that requires ongoing attention. Regulations continue tightening globally, and any persistent identifier needs a documented legal basis, user-facing transparency, and a deletion pathway. Get those pieces right, and yehidomcid97 becomes a reliable backbone for cross-platform analytics, feature management, and observability.