Every three months, your sophisticated firewall becomes outdated. Every six months, your security protocols need revision. Every year, your entire defense strategy requires overhaul. This is the brutal reality of traditional system architecture in an era where cyber threats evolve faster than human analysts can respond. CHAS6D offers a fundamental departure from this endless arms race—a framework designed not merely to defend against today’s threats but to adapt autonomously to tomorrow’s unknown challenges.
This comprehensive guide demystifies CHAS6D (Cybernetic Hierarchical Adaptive Systems in Six Dimensions), exploring its origins, architectural components, real-world applications, and strategic implementation. Whether you are a systems architect seeking to future-proof your infrastructure, a CISO evaluating next-generation security frameworks, or a business leader exploring digital transformation pathways, this analysis provides actionable insights backed by industry research and emerging best practices.
What is CHAS6D? Understanding the Framework
Answer Capsule: CHAS6D stands for Cybernetic Hierarchical Adaptive Systems in Six Dimensions. It is a conceptual framework for building self-regulating, intelligent digital systems that can think, adapt, and evolve across six critical dimensions while ensuring security and efficiency. Unlike traditional static architectures, CHAS6D embeds feedback loops and adaptive mechanisms directly into the system foundation.
At first glance, CHAS6D might appear as just another tech acronym in an industry saturated with frameworks and methodologies. However, this distinction warrants closer examination. CHAS6D represents a synthesis of disciplines that have historically operated in silos: cybernetics, systems theory, artificial intelligence, and secure computing [1].
The framework emerged from advanced research in cybernetic modeling and distributed intelligence, with early implementations targeting complex environments where adaptability and security were paramount—military defense logistics, healthcare systems, and critical infrastructure [2]. These high-stakes applications demonstrated that traditional hierarchical structures excelled at routine tasks but failed catastrophically when confronted with novel scenarios [3].
CHAS6D addresses this fundamental limitation by treating adaptability not as an add-on feature but as a core architectural principle. The framework crystallized from interdisciplinary research recognizing that rigid hierarchies, while efficient under stable conditions, require fundamental redesign when environment assumptions change. The solution involves creating systems that treat change not as an interruption but as a primary input for continuous adaptation [3].
Core Components of CHAS6D
The CHAS6D framework comprises five interconnected components that work synergistically to deliver robust, scalable, and intelligent systems:
- C (Cybernetic): Feedback-driven systems enabling self-regulation and continuous adjustment through real-time feedback loops at every layer
- H (Hierarchical): Multi-layered structures distributing logic and authority across levels for organized functionality and fault isolation
- A (Adaptive): Dynamic capabilities allowing systems to respond to both predefined rules and unpredictable anomalies through machine learning and dynamic reconfiguration
- S (Systems): Integrated components working collaboratively toward shared objectives rather than isolated functions
- 6D (Six Dimensions): Six analytical layers—structural, behavioral, adaptive, temporal, semantic, and security—providing comprehensive optimization, monitoring, and protection
Unlike proprietary software solutions, CHAS6D functions as an open conceptual model and thought-leadership framework that can be implemented across virtually any technology stack [4]. This platform-agnostic characteristic distinguishes it from vendor-locked alternatives and explains its growing adoption across diverse industries.
The Six Dimensions Explained: A Deep Dive
Answer Capsule: The six dimensions—structural, behavioral, adaptive, temporal, semantic, and security—represent six critical lenses through which CHAS6D analyzes and optimizes system behavior. Each dimension addresses a specific functional area, ensuring no critical aspect gets overlooked during design or operation. Together, they create systems that perceive, reason, and respond holistically rather than in isolation.
Understanding each dimension individually reveals how CHAS6D achieves its comprehensive approach to system design:
1. The Structural Dimension
The structural dimension concerns the physical and logical architecture of systems—codebase organization, hardware setup, network topology, and component connections. In CHAS6D, structure transcends mere organization; it emphasizes creating architectures that can evolve without disintegration.
Traditional systems often suffer from tight coupling, where changing one component requires rewriting interconnected modules. CHAS6D advocates for modular, loosely coupled structures enabling independent component updates or replacements without system-wide disruption. This architectural principle directly impacts maintainability, scalability, and long-term viability.
2. The Behavioral Dimension
Behavioral dimensions focus on how systems interact with users and other systems—user experience, API design, communication protocols, and external presentation. A system can be internally perfect yet fail catastrophically if it behaves unpredictably from user perspectives.
CHAS6D requires continuous behavioral monitoring in real-world conditions rather than solely within controlled test environments. This dimension ensures systems maintain helpful, consistent interactions while adapting to diverse user patterns and expectations.
3. The Adaptive Dimension
The adaptive dimension encompasses machine learning capabilities, dynamic rule adjustment, and environmental responsiveness. However, CHAS6D’s adaptive principle extends beyond algorithmic components to encompass entire architectural adaptability.
In practice, this means an e-commerce platform would not solely rely on machine learning for product recommendations. It would also adapt database queries based on traffic patterns, modify caching strategies based on user behavior, and adjust error handling based on failure analysis. The entire organism learns, not just specific algorithms [5].
4. The Temporal Dimension
Temporal dimensions address time-based considerations—real-time processing, historical data tracking, scheduled tasks, and time-sensitive decision-making. This recognition that timing critically impacts technology outcomes distinguishes CHAS6D from static frameworks.
A fraud detection system identifying suspicious activity three days later proves useless. A backup system running exclusively during peak hours creates operational problems. CHAS6D compels explicit consideration of when events occur, their duration, and system behavior across varying time scales [5].
5. The Semantic Dimension
The semantic dimension deals with data interpretation, context, meaning, and ontologies—transforming raw data into actionable intelligence. Raw data without interpretation remains meaningless; this dimension ensures systems understand information significance beyond mere format.
For instance, two users entering “500” into a field carry completely different implications depending on whether one enters age versus credit limit. CHAS6D incorporates knowledge graphs and context-aware processing, enabling decisions based on genuine understanding rather than simple pattern matching [5].
6. The Security Dimension
Security in CHAS6D differs fundamentally from traditional approaches. Rather than treating security as an afterthought or separate layer, CHAS6D integrates protection into every dimension:
- Structural Security: Encrypted pathways, secure boot procedures, tamper-resistant components
- Behavioral Security: Machine learning anomaly detection, unusual pattern identification
- Adaptive Security: Dynamic auto-patching and reconfiguration minimizing exposure during active threats
- Semantic Security: Contextual analysis identifying misinformation or suspicious content
- Temporal Security: Forensic timelines enabling detailed security event analysis
This integrated approach ensures CHAS6D-based systems remain resilient against known threats while adapting to emerging risks in increasingly complex digital landscapes [1].
CHAS6D vs Traditional Architectures: A Comprehensive Comparison
Answer Capsule: CHAS6D differs fundamentally from traditional architectures through embedded adaptability, integrated security, and multi-dimensional analysis. While traditional frameworks treat security, scalability, and intelligence as separate concerns to be added later, CHAS6D weaves these requirements into the foundational design, creating systems that self-heal, self-optimize, and evolve autonomously.
Organizations evaluating CHAS6D frequently request comparison against established frameworks. The following analysis addresses this need directly:
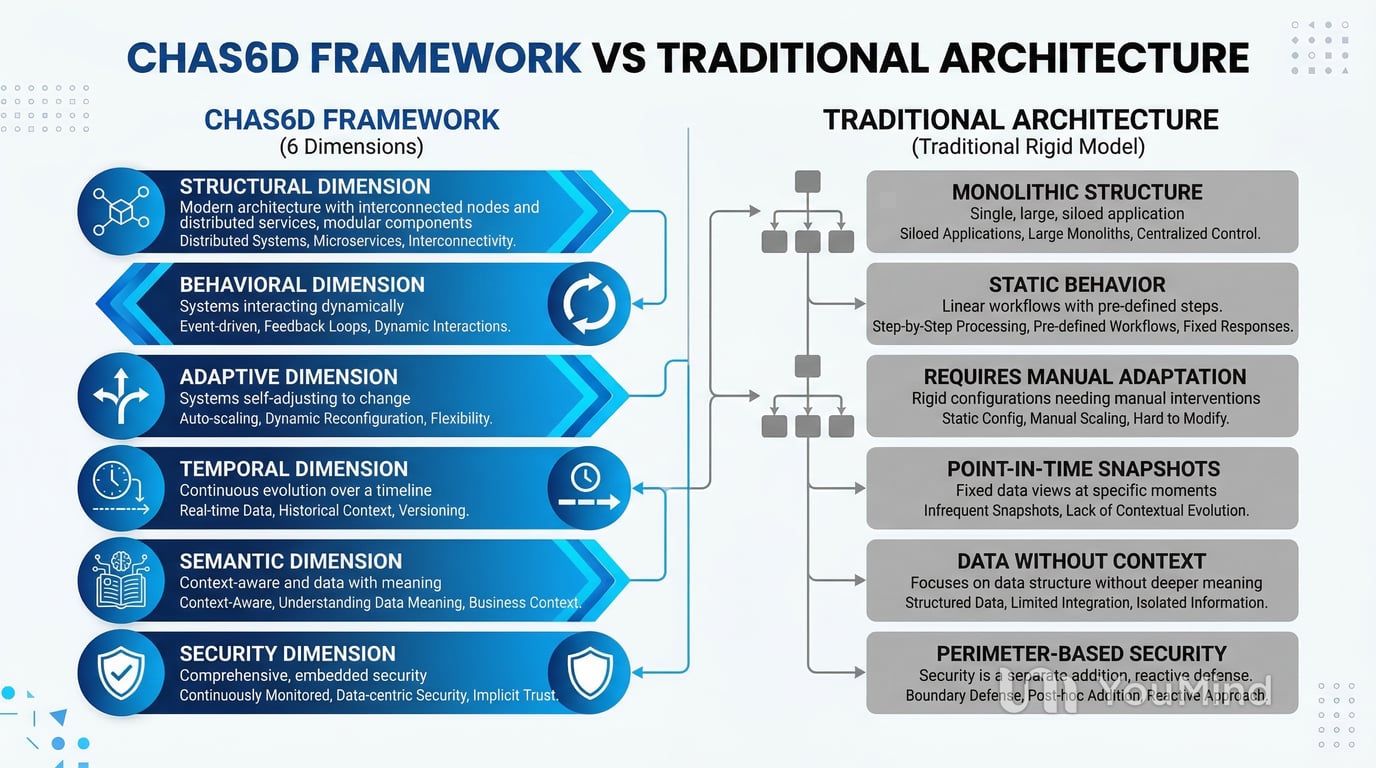
| Dimension | Traditional Architecture | CHAS6D Framework |
|---|---|---|
| Adaptability | Static rules requiring manual updates; adaptation bolted on as afterthought | Embedded feedback loops enabling autonomous adaptation to changing conditions |
| Security Model | Perimeter-based defense; reactive responses to known threats | Integrated security-by-design; proactive threat modeling across all dimensions |
| Scalability | Vertical scaling; hardware-dependent expansion | Horizontal scaling with hierarchical distribution; elastic resource allocation |
| Data Interpretation | Format-focused processing; limited contextual understanding | Semantic analysis with ontology-based context awareness |
| Time Handling | Point-in-time processing; limited historical analysis | Temporal awareness with event sourcing and trend analysis |
| Failure Response | Manual intervention required; system downtime during recovery | Self-healing capabilities; automated failover with minimal disruption |
| Decision-Making | Centralized control points; single decision authority | Distributed hierarchical logic; local autonomy with global coherence |
Organizations implementing CHAS6D principles report not incremental improvements but step-change advancements in system integration speed, threat response, and operational agility [3]. A mid-sized financial firm CISO implemented CHAS6D-inspired security architecture and detected three sophisticated attacks within six months that previous generation tools completely missed—attacks recognized through subtle behavioral deviations rather than known signatures [5].
Real-World Applications and Case Studies
Answer Capsule: CHAS6D finds applications across cybersecurity, autonomous vehicles, smart cities, healthcare, and financial services. In healthcare, CHAS6D-enabled systems reduced patient readmissions by 40% through continuous adaptive monitoring. Financial institutions report 60% maintenance cost reductions after two years of CHAS6D-based platform operation.
While competitors offer only theoretical applications, documented implementations demonstrate concrete outcomes:
Healthcare: Personalized Medicine at Scale
Traditional electronic health records function as static databases. CHAS6D-based health systems continuously monitor patient data from wearables, lab results, genetic information, and environmental factors, adapting treatment recommendations based on individual patient responses to medications and predicting health deterioration before it becomes critical [5].
A hospital system implementing CHAS6D principles in their care coordination platform reduced patient readmissions by 40%—an outcome directly attributable to the framework’s adaptive capabilities [5]. This demonstrates how CHAS6D transforms reactive healthcare delivery into proactive, personalized medicine.
Financial Services: Real-Time Fraud Detection
Financial algorithms represent CHAS6D’s most mature application domain. High-frequency trading systems have utilized CHAS6D-like approaches for years, but the framework now extends to broader financial services:
- Fraud detection systems adapting to new scam techniques in real-time
- Credit risk models adjusting based on changing economic conditions
- Investment algorithms learning from market patterns while maintaining strict risk controls
The semantic dimension proves particularly crucial in finance—understanding that transactions are suspicious not merely based on amount but considering context, timing, and relationship to other activities [5].
Smart Cities: Urban Infrastructure Integration
Modern cities comprise thousands of interconnected systems—traffic lights, power grids, water systems, emergency services, and public transportation—that traditionally operated in silos. CHAS6D enables true integration.
When a traffic accident occurs, CHAS6D-enabled infrastructure automatically adjusts traffic light timing to accelerate emergency vehicle arrival, reroutes public transit to avoid affected areas, alerts hospitals to prepare for potential casualties, and adjusts power grid loads if infrastructure is affected—all adaptively based on real-time conditions rather than following fixed emergency protocols [5].
Implementing CHAS6D: A Phased Roadmap
Answer Capsule: Successful CHAS6D implementation requires a phased approach: Foundation Phase (Months 1-3) focuses on audit and architecture design; Integration Phase (Months 4-6) involves pilot projects and team training; Optimization Phase (Months 7-12) enables full deployment with continuous learning. Organizations report 60% lower maintenance costs after two years compared to traditional systems.
Organizations cannot achieve true adaptability while clinging to rigid project management practices or static requirement documents. Implementation requires fundamental changes in technology thinking and organizational processes [5].
Phase 1: Foundation (Months 1-3)
- Audit existing systems against the six dimensions
- Identify structural gaps, security weaknesses, and adaptation limitations
- Assemble cross-functional implementation team
- Design target architecture aligned with CHAS6D principles
- Establish baseline metrics for success measurement
Phase 2: Integration (Months 4-6)
- Deploy pilot projects on non-critical systems
- Train architects and engineers in cybernetic principles
- Implement initial feedback loops and monitoring systems
- Refine architecture based on pilot learnings
- Begin semantic and temporal dimension implementation
Phase 3: Optimization (Months 7-12)
- Expand to enterprise-wide deployment
- Activate remaining dimensions systematically
- Implement semantic bridges between CHAS6D and legacy systems
- Establish continuous improvement processes
- Measure and document ROI achievements
Investment Analysis: Total Cost of Ownership
Initial CHAS6D implementation demands significant upfront investment in skilled architects, infrastructure supporting real-time feedback, and team training. However, long-term cost dynamics favor CHAS6D approaches:
| Cost Category | Traditional System (Annual) | CHAS6D System (Annual) |
|---|---|---|
| Initial Development | $500,000 | $750,000 |
| Maintenance Labor | $200,000 | $80,000 |
| Security Updates | $150,000 | $50,000 |
| Downtime Costs | $100,000 | $20,000 |
| Year 2 Total | $950,000 | $900,000 |
| Year 3 Total | $950,000 | $150,000 |
One technology director reported that after two years of operating a CHAS6D-based platform, maintenance costs were 60% lower than their previous traditional system, while uptime improved from 99.5% to 99.99% [5].
The Security Dimension: Beyond Traditional Cybersecurity
Answer Capsule: CHAS6D treats security as foundational DNA rather than an add-on feature. The framework embeds protection mechanisms across all six dimensions—structural encryption, behavioral monitoring, adaptive threat response, temporal forensics, and semantic threat analysis—creating defense-in-depth that evolves proactively against emerging threats.
Traditional security approaches operate reactively, responding to known attack patterns. CHAS6D’s security dimension establishes proactive defense mechanisms embedded throughout the entire system architecture [1].
Predictive Security Modeling
CHAS6D-based security systems learn normal patterns within specific environments and detect anomalies based on behavioral deviations rather than relying solely on signatures of known attacks [5]. This approach catches sophisticated attacks that signature-based systems miss entirely.
Self-Healing Security Mechanisms
When threats are detected, CHAS6D systems respond dynamically rather than executing static responses. The adaptive layer simultaneously adjusts multiple defenses—requiring additional authentication for affected accounts, throttling transaction speeds to limit damage, alerting security teams with context-rich information, and updating threat models to catch similar attacks faster in future [5].
Following any security incident, CHAS6D incorporates learnings across all dimensions. Structural layers add new monitoring points. Behavioral layers update models of normal user activity. Semantic layers refine understanding of attack indicators. The entire organism becomes more resilient, not merely patched for specific vulnerabilities [5].
Challenges and How to Overcome Them
Answer Capsule: CHAS6D adoption faces challenges including complexity management, skill requirements, initial investment, and organizational change resistance. Success requires executive sponsorship, phased implementation, continuous team training, and treating CHAS6D as a fundamental architectural shift rather than another methodology layer.
Despite its innovative capabilities, CHAS6D faces adoption obstacles requiring strategic navigation:
Managing Complexity
Designing systems across six dimensions demands advanced technical expertise spanning cybernetics, AI, systems theory, and full-stack development [1]. Solution: Begin with experienced architects and partner with consulting organizations specializing in adaptive systems.
Initial Investment Requirements
Implementation demands significant upfront investment in technology and training. Solution: Start with pilot projects demonstrating quick wins before enterprise-wide commitment, building organizational confidence through demonstrated results.
Limited Off-the-Shelf Tools
Few vendor products are specifically designed for CHAS6D principles. Solution: Treat CHAS6D as a design philosophy rather than a product purchase, selecting and configuring existing tools to align with framework principles [5].
Organizational Change Resistance
The most common mistake involves treating CHAS6D as merely another methodology to layer atop existing practices. Solution: Prepare for fundamental process changes, not just technology updates—cultural transformation proves as important as technical implementation [5].
The Future of CHAS6D in Enterprise Technology
Answer Capsule: CHAS6D principles will become standard practice within five years, following trajectories similar to agile development and cloud computing adoption. Early adopters—currently implementing CHAS6D in AI governance, autonomous systems, and smart infrastructure—will gain significant competitive advantages through superior system adaptability and resilience.
Emerging CHAS6D application areas include AI governance models ensuring artificial intelligence systems operate ethically and safely, ethical robotics creating machines making responsible decisions in ambiguous situations, decentralized autonomous organizations (DAOs) enabling self-governing digital entities, and space-based systems managing satellite constellations requiring autonomous decision-making [1].
Industry and academia collaborate toward standardizing CHAS6D as the architectural foundation for next-generation technologies [1]. As digital infrastructure becomes increasingly critical to every business and life aspect, demand for systems evolving and adapting as quickly as surrounding conditions will intensify.
Organizations beginning CHAS6D learning and implementation now will possess significant advantages over competitors waiting for framework maturation. The question is no longer whether CHAS6D will become standard practice but how quickly your organization can adapt to embrace its principles.
Frequently Asked Questions
What does CHAS6D stand for?
CHAS6D stands for Cybernetic Hierarchical Adaptive Systems in Six Dimensions. It represents a comprehensive framework for designing digital systems capable of self-regulation, learning from experience, and adapting to changing conditions across six critical dimensions: structural, behavioral, adaptive, temporal, semantic, and security.
Is CHAS6D a software product I can buy?
No, CHAS6D is not a specific software product or platform. It functions as a design philosophy and architectural framework applicable using various technologies and tools. Similar to agile methodology—you cannot purchase agile software, but you can implement agile principles using tools fitting your specific needs [5].
How does CHAS6D differ from traditional system design?
Traditional systems follow fixed rules and require manual updates for handling new situations. CHAS6D systems incorporate feedback loops and learning mechanisms enabling automatic adaptation. They organize hierarchically to manage complexity and optimize across six dimensions rather than focusing narrowly on specific metrics.
What industries benefit most from CHAS6D?
While CHAS6D principles can apply to any technology system, they prove particularly valuable in cybersecurity, autonomous systems, financial services, healthcare, smart infrastructure, and domains where conditions change rapidly and system failures carry serious consequences [5].
Do I need to be an expert in cybernetics to use CHAS6D?
No, but understanding core principles is essential. The learning curve proves significant, but many resources exist for beginners. Start with foundational concepts and gradually apply them to your specific domain—practical experience teaches more than theoretical study alone [5].
How long does CHAS6D implementation take?
Timelines vary enormously based on scope. Small projects might adopt CHAS6D principles within weeks, while enterprise-wide transformations could take years. Most organizations benefit from gradual approaches—applying CHAS6D to new systems first and gradually refactoring legacy systems over time [5].
Is CHAS6D more secure than traditional approaches?
Security constitutes one of CHAS6D’s six dimensions, making it inherently more secure than traditional approaches treating security as an afterthought. The framework emphasizes security-by-design with adaptive threat response and comprehensive monitoring across all system layers [1].
What is the learning curve for CHAS6D?
The learning curve is significant, requiring understanding of cybernetics, systems theory, adaptive algorithms, and security principles. Organizations should plan for 3-6 months of dedicated learning before attempting significant implementations, with ongoing education as the framework evolves.
Can existing systems be migrated to CHAS6D?
Yes, though migration requires careful planning. Begin by auditing current systems against the six dimensions to identify gaps. Implement semantic bridges between CHAS6D-managed environments and legacy systems, treating rigid APIs as temporary interfaces during transition [3].
What is the future outlook for CHAS6D?
CHAS6D principles will become standard practice within five years, mirroring the adoption trajectory of agile development and cloud computing. Organizations implementing these concepts now will possess significant competitive advantages through superior system adaptability and resilience [5].
References
- CHAS6D Official Site. “What is CHAS6D? – All In One Guide For Beginners in 2025.” https://chas6d.com/
- Purdue Stats. “CHAS6D: Cybernetic Systems in Six Dimensions.” https://purduestats.com/chas6d-cybernetic-systems-in-six-dimensions/
- Peruse Magazine. “Chas6d: The Adaptive Digital Architecture Redefining Enterprise Resilience.” https://perusemagazine.com/chas6d/
- NovaBiz Technology. “What is Chas6d? 6D Cybernetic Adaptive System Explained (2026 Guide).” https://novabiztechnology.com/what-is-chas6d/
- Tekiila. “What Is CHAS6D? A Complete Beginner’s Guide to Cybernetic Hierarchical Adaptive Systems in Six Dimensions.” https://tekiila.com/chas6d/










